Cybercriminals, Debit Cards, Credit Cards, And Underground Markets
This blog post covers one way cybercriminals profit from moving stolen financial data, and why you should always use a secure payment processor on checkout pages.
Disclaimer: This post on cybercrime is for research and education only. The author does not endorse illegal activities. Engaging in cybercrime is illegal and punishable by law. Use this information responsibly and ethically.
My Personal Journey
As a reformed black hat hacker, I've witnessed the methods and techniques that cybercriminals use to access and transfer financial data. In this blog post, I will provide an overview of how attackers discover and exploit vulnerabilities in web applications and how they profit from the stolen data.
My aim is to offer insight into the world of cybercrime and encourage consumers to choose secure payment options at checkout, rather than picking one carelessly.
Step 1: Identifying a Target
The attacker begins by searching for a random website on the internet, typically focusing on sites likely to contain financial data, such as hotel chains or small businesses. They then examine the payment page to determine if it uses a payment processor. If not, the website becomes a prime target for exploitation. For example, if targeting hotel chains in France, they could use the following method:
site:fr inurl:"hotel" ext:php OR ext:asp OR ext:aspx OR ext:cfm OR ext:cgi OR ext:jsp
You might wonder if this approach only yields easy targets. In reality, not necessarily. At this stage, the attacker is merely searching for French hotel chains with extensions indicating web-pages likely to host dynamic content with a database. It's a mapping process, and they're not yet looking for vulnerabilities.
Step 2: Gaining Access to Financial Data
After selecting a target, the attacker works on hacking the web application to gain access to its database. In some cases, financial data might not be stored securely, making it easier for the attacker to obtain and use the stolen data. In this particular method, they would use a standard black-box approach to audit the web application for vulnerabilities and find a way in.
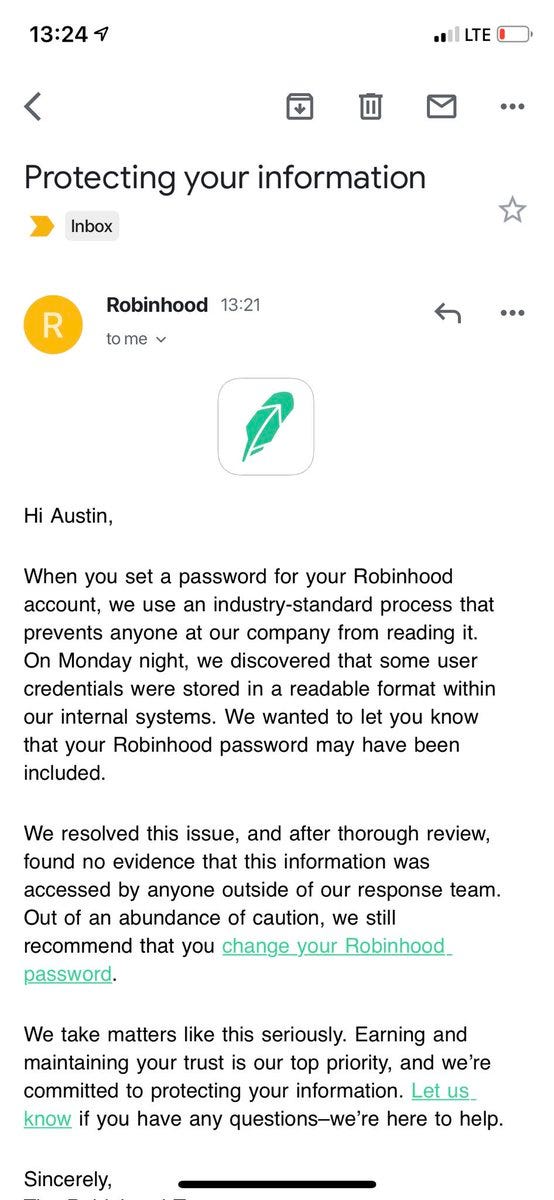
Believe it or not, a ton of websites still store financial data in plaintext format, which is a significant security risk. In addition, some websites use weak encryption algorithms like MD5 to protect sensitive data, which can easily be cracked in hours. All you’ve got to do is take a lot of the leaks out there and you’ll see it for yourself.
Step 3: Parsing and Verifying the Stolen Data
So, after successfully breaching a web application and obtaining financial data, the attacker will typically format the data into a file, which involves separating the fields with a pipe delimiter and removing any expired cards. This process ensures that only valid records are retained (please note these are fake records I generated):
VISA | 4916489266798339 | 2/2025 | David Foster | United Kingdom
VISA | 4532158521752761, 2/2030 | 540 | Frank Martinez | United States
VISA | 4556156743188823 | 6/2024 | 954 | Edward Vaz | Germany
VISA | 4916971424049507 | 11/2028 | 475 | Helen Baker | United Kingdom
To format the data, the attacker may use text manipulation tools like grep, sed, and awk on Linux systems. Alternatively, they can use a text editor such as NotePad++ to do it.
Step 4: Selling the Data
The attacker then contacts a market owner, typically through networking or a recommendation from someone who can vouch for their credibility. Many market owners are particular about their partners, so a solid reputation or multiple vouches are essential.
The market owner selects 10-20 random samples from the data dump and verifies their validity using a tool like Stripe's API. If a certain percentage of the records are valid, the market owner may choose to purchase the entire dump or grant the attacker a vendor account on their platform.
The offered price depends on various factors, such as the available columns, the types of debit or credit cards, and the country they originate from. For instance, a database or "base" of debit and credit cards from a Spanish hotel chain will not command the same offer as one from an American hotel chain.
Profits from sales are subsequently split between the attacker and the platform. For more information on these types of markets, have a read of this:


It covers a major financial data store that many cybercriminals use regularly.
Step 5: Monetizing the Data
Ultimately, the stolen financial data is sold to various individuals for different purposes. It's not uncommon for thousands of records to be sold within 24 hours, making this a lucrative endeavor for the attacker and market owner.
From my past observations, the market owner often makes the most money, but they also take the most significant risk by running a financial cybercrime empire. At the other end of the spectrum are the people who commit fraud using the stolen data, facing considerable risk as well.
Personal Example and Takeaways
During my time in cybercrime, I observed various techniques attackers employed to exploit and monetize stolen financial data. One example involved an attacker who controlled a server and set up a scheduled task to transfer all new records every week. This seemingly endless income stream underscored the potential profitability of such cybercrime.
Banks typically initiate investigations and pinpoint the common source of the stolen financial data only when the records are used frequently and draw attention, and even then, the attacker must be moving thousands of records. A mere few hundred records are unlikely to prompt banks to launch an investigation.
It's important to note that the method described in this blog post is just one of many ways attackers can move stolen financial data. Cybercriminals employ numerous other techniques and strategies to exploit vulnerabilities and profit from stolen data.
Attackers can phish for financial data
Attackers can compromise point-of-sale (POS) machines for stolen data
Attackers can install skimmers on physical devices
The possibilities are virtually endless, but this blog post demonstrates how many people profit from this type of crime through just one technique. The chain goes on for quite some time.
The attacker profits, the market owner profits, and the people purchasing the financial data profit. Sometimes, intermediaries between the attacker and market owner charge a commission just for connecting someone who can move the financial data.
As a consumer, it's much safer to choose a payment processor when possible on a checkout page, rather than blindly entering your debit or credit card information.
You might think this sounds far-fetched, but the security of some web applications is alarmingly poor, and I would never trust a small business or website to keep my financial information secure, regardless of their intent because they just don’t have the experience to keep it secure.
On a final note, next month, I'll be writing an article on how effortlessly one can go from an IP address to an individual's complete information within minutes, using publicly leaked datasets.
To prevent the post from being misused as a cybercrime guide, considering the actionable information it contains, I’ll be placing it behind a paywall (which is above).